A: Matching Port Numbers with ACLs 1
First, think of TCP headers, and the source port and destination port. Then think about the predictable port – the well-known port – and whether it will be the source or destination port. Then think about the syntax of the ACL command… and the location + direction of the ACL. Got all that? Well, you needed it to answer this latest question. Check this post for details, and the question post for the challenge!
Answer
E
Explanation
To answer this question, you have to piece together several facts, with no pre-set order:
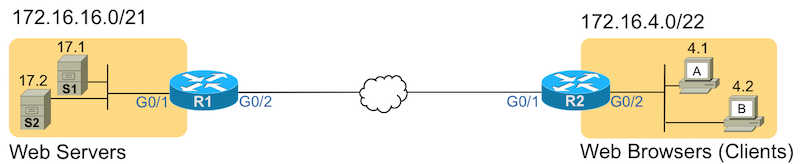
First, determine the well-known port, and whether the sending host will use the well-known port as the source or destination port in the TCP header. In this case, the question stem tells us that the message to match flows from the servers (on the left) to the clients (on the right). Regardless of their location in the figure, because the server sends the message, the server uses its port number as the source port number. The sending server then uses the web clients’ (web browsers) port numbers as the destination port numbers, respectively.
Next, think about the predictable port number – the well-known port – used by the server application. The stem mentions unencrypted web traffic, which uses port 80. A reference to encrypted web traffic would mean that the connection uses SSL, which uses well-known port 443.
You also need to consider the location and direction of the ACL, but the wording of the question stem may have already told you what direction to use. The stem states that the ACL will be added to router R1, on its G0/1 port, for the input direction. Those details confirm that the ACL would match packets coming from the server going to the clients.
Because the ACL needs to match packets sent by the web servers, the ACL command must match the source port field, and not the destination port field. The destination port field will list a dynamic port number (49,152 and above) whose value is unpredictable. To match the source port, the command must include eq www or eq 80 (which IOS changes to eq www). Additionally, to match the source port field, the eq www keywords need to be before the destination address field(s) in the command, not after.
Finally, the command must use a tcp keyword, not an ip keyword. When using the ip keyword, IOS does not allow matching of any transport layer header fields – in fact, IOS would reject the two answers that use an ip keyword with syntax errors.
All those facts together give you enough information to choose the correct answer, but you might also care to think about the source and destination IP address fields for a moment. In this case, all answers used the same source address + mask combination and same destination address + mask combination. Each matches the source subnet of 172.16.16.0/21, with a destination subnet of 172.16.4.0/22.
In summary, the correct answer (E) uses the tcp keyword and includes the eq www parameters between the source and destination IP address parameters (matching the source port).
Sifting Through the Distractors and Common Mistakes
Questions that ask about matching messages based on TCP or UDP ports provide exam question authors plenty of opportunities to create effective distractors. This question used a few of the classic cases. To summarize some of those:
- The command must use tcp or udp keywords, not ip, to allow the matching of port numbers.
- You must think about the direction of the message in relation to the ACL location and direction, and ask:
- If the ACL examines a message sent by the server, compare the source port
- If the ACL examines a message sent to the server, compare the destination port
- The command does not use a keyword to identify whether the port-matching parameters refer to the source or destination port. That is, you must memorize:
- To match the source port in the message, put the port matching parameters between the source and destination address fields
- To match the destination port in the message, put the port matching parameters after the destination address fields.
That’s it! For further exercise, if interested, change the packet direction, location/direction of the ACL, and the application, and try to determine what you would configure.
