#CCENT and #CCNA Fast Start: Port Security
Port Security used to be spread across both halves of #CCNA (both ICND1 and ICND2). With the new exam updates, it’s all in one place, over in the ICND1/CCENT side of the equation. Today’s post gets us started with a quick look at this tricky little feature.
The Exam Topics: Old and New
As usual, for those of you still thinking through the old version new exam thing, here’s a quick breakdown. The old exams specifically mentioned port security in two exam topics, one each for ICND1 and ICND2, as follows. For ICND1:
- Implement and verify basic security for a switch (port security, deactivate ports)
…and for ICND2:
- Implement basic switch security (including: port security, unassigned ports, trunk access, etc.)
For the new exams, as usual, Cisco has given us more details, with these ICND1 exam topics:
Configure and verify Switch Port Security features such as
- Sticky MAC
- MAC address limitation
- Static / dynamic
- Violation modes
- Err disable
- Shutdown
- Protect restrict
- Err disable recovery
As usual, don’t over read the extra detail to mean that Cisco intends to cover more detail. Cisco likely didn’t add a bunch of topics to the new exam for Port Security; they just gave us more detail about what’s there. Plus, they happened to put it all into ICND1.
Port Security Overview
Cisco switches, using default settings, want to forward Ethernet frames. When you buy a Cisco switch, remove it from the box, plug in the cables and power it up, it forwards Ethernet frames. Port Security then gives the network engineer a tool to limit what frames a switch forwards, making the network more secure.
Port security revolves around one basic observation about the addresses used in Ethernet frames: The source MAC address of an Ethernet frame identifies the device that sent the frame onto the LAN. Literally, Port Security makes choices based on the source MAC address, but conceptually, it makes choices based on which device sent the frame onto that particular Ethernet LAN.
Beyond the basic concept of checking the identity of the sender of the frame, Port Security lets the network engineer choose many basic settings for a port, like:
- How many different MAC addresses (aka, difference sources of Ethernet frames) can send frame INTO this port
- The specific MAC addresses of the host allowed to send frames into that port
- What to do when an incoming Ethernet frame breaks the rules (shutdown the port, discard only offending traffic, with various notifying messages)
Just for a quick flavor for the big picture design, figure 1 shows a small LAN. The switch on the left has four ports on the right. Three ports connect to a single device each, so the network engineer could use port security, allow only frames sent from the one known MAC address, and strictly lock down those ports. The bottom port, which connects to another switch, could be limited to a volume of different MAC addresses used as the source for different frames. For instance, if there should be no more than 20 devices on switch SW2, the configuration could limit the number of MAC addresses, while not specifying each MAC address.
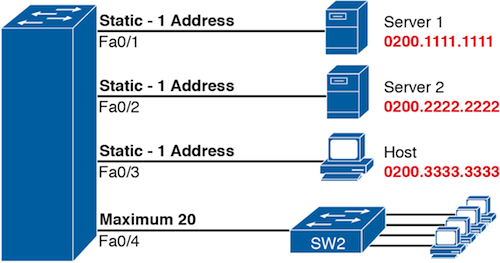
Figure 1: Sample Uses for Port Security
More on Port Security
One of the challenges with Port Security that it’s easy to miss the core functions while getting distracted by all the optional features. Next post, I’ll list a sample Port Security question that sticks with the core default features.

[…] Link to the brief topic introduction […]
[…] Introduction to this topic as it exists in the new CCENT and CCNA exams: […]