Password Config Question
Here’s a new CCENT question to consider. It’s a bit long to read, but it reviews some unrelated concepts, so hopefully the length won’t get in the way. As usual, if you post ideas, leave out your answer letters from the title line to avoid spoiling it for others. Enjoy! Question is below the fold.
The figure shows a small enterprise network. The switches all have default configuration, except for the configuration to be added to switch SW1, as shown a little later in the question. Host A has a working terminal emulator that supports both telnet and SSH. Host A also has a console cable connected to SW1’s console port (not shown in the figure). The other two switches both have all default configuration, except that SW3 configures all ports to be in VLAN2.
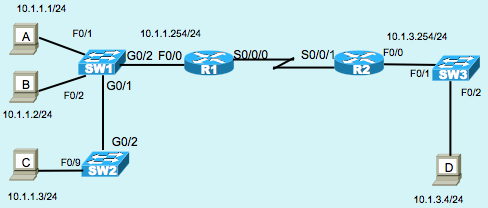
Although these questions mostly ignore the routers and PCs, note that all PCs can ping each other. On the left side of the figure, all switch interfaces default to be in the same VLAN (VLAN 1). Similarly, on the right, all devices sit in the same VLAN (VLAN 2).
The switches are layer 2 only switches, like most typical Cisco access layer switches.
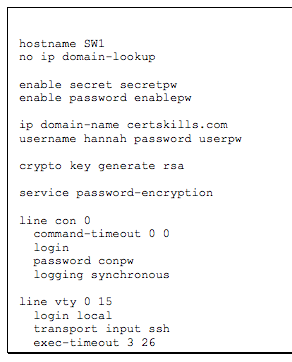
The following configuration is next copied and pasted into configuration mode on SW:
Example 2-2-1: Configuration To-be-Pasted into Switch SW1
The question:
After pasting the configuration into configuration mode, the engineer exits configuration mode, and issues the show running-config command. Which of the following is true about the enable, enable secret, console password, and the password set on the one username command?
A. The enable secret password, secretpw, is visible
B. The enable password, enablepw, is visible
C. The password in the username command, userpw, is visible
D. All of these passwords are hidden from view, but with only some listing an encryption or encoding type 7 in the command
E. All of these passwords are hidden from view, with all listing an encryption or encoding type 7 in the command

Hi Mr Odom, answer is “D”
Enable secret listing encryption type 5, meaning it’s encrypted with MD5 algorithm, all others encrypted with weak encryption and they listing 7 in the running config.
Thank’s for great books!
Thanks Dadash! Glad you liked the books!
Wendell
Answer is D. The best way to confirm this is to use GNS3 or actual gear, enter the service password-encryption command, configure the passwords, and run the show run command. You will see the output exactly as stated by dadash above.
Encoding passwords with Type 7 is weak because tools exist that can decode these passwords in the twinkling of an eye. They’re mainly useful to avoid leaving them in cleartext and hence allowing someone looking over your shoulder to see them in case you displayed the running config.
Definitely answer D
The answer is very simple. All the line login pass, username pass and enable passwords will be encrypted, by effect of the “service password-encryption” command. The simple passwords (writing “password” in the respective line command) will be listed preceded by 7, indicating a weak protection. The secret passwords (writing “secret” in the line command) will be listed with a 5, indicating a little more strong encryption with MD5 hash. More low number listed, indicates a more strong encryption.
For example, New IOS can use SHA-256 hash for routers, a more strong ecryption, listed with a 4 previously.
One best practice is try to use always “secret” pass, for login local with “username xxx secret yyyy” when is possible, instead “username xxx password yyyy”.
Thanks for all the great answers, folks!
I’ll post the official answer tomorrow. In the mean time, I’ll let it run for anyone who wants to view the question with fresh eyes.
Thanks!
Wendell
Hi Mr. Odom,
The answer to this question has been moved to chapter 34, but the question itself is still linked under chapter 8.
Thank you!
Alaa
Hi Wendell,
Not sure if something has happened to the webpage, but I can’t see the configuration which is to be applied to SW1.
“The following configuration is next copied and pasted into configuration mode on SW:
Example 2-2-1: Configuration To-be-Pasted into Switch SW1
The question:”
Is that right?
Hi Bav,
Thanks. It was an incorrect link. I migrated to a new blog platform a few months back, and it moved from Linux to Windows… which introduced case sensitivity… so it broke a bunch of links. We missed that one – thanks for the heads up. Should be fixed now.
Wendell