ACL Practice Drills
You need practice with ACLs for CCENT and CCNA R/S. Some of that practice should focus on putting a complete ACL together, with multiple Access Control Entries (ACE) (that is, multiple permit and deny commands) to meet a set of requirements. But even before building complete ACLs, you need to master the basics of building a single ACE (that is, a single command).
This post introduces a type of exercise in this blog: the ACL Drill. These exercises let you practice the various steps of creating ACL commands. This post describes the basic process, with some advice on how to approach creating ACL commands, both for these drills and for the exams.
One ACE ACL
In Cisco-speak, one line in an ACL is called an Access Control Entry (ACE).
Some of the drills give you practice with building an ACL with a single ACE, keeping the focus of the discussion on one command (ACE) at a time. Basically, for each stated problem, you have to create one ACE – specifically either a permit or deny command for a named ACL – that meets the criteria.
Example One ACE ACL Drill
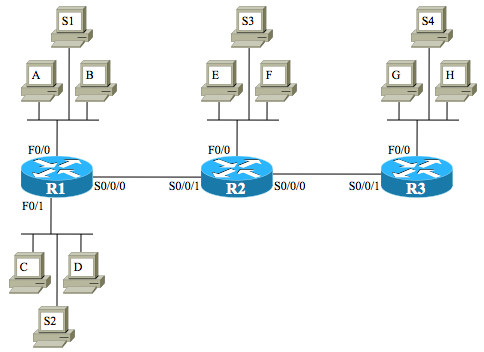
For the ACL practice drills in this blog, we will frequently use the following diagram. The IP addresses and subnets will change, even from question to question. In some cases, you will match traffic going from a client to a server, and sometimes you will stop traffic as it goes from a server to a client. In those cases, you will need to think about the placement of the port number fields.
For example, a drill question might state:
Host A (10.1.1.1/24) attempts to connect to web server S4 (192.168.2.254/27). Your ACL will be applied outbound on R2’s S0/0/0 interface. Permit traffic from host A’s subnet to reach the web service on S4.
First, consider the location of the ACL. The problem statement asks that you enable it outbound on R2’s S0/0/0. That placement means it will filter packets as they pass from host A to server S4. So, any matching of host A’s IP address should happen as the source IP address, and any matching of server S4 should happen as the destination address. If the requirement stated that the ACL was inbound on that same interface, you could still permit the traffic, but you must do so by matching traffic sourced from the server, sent back to host A.
Matching Subnets
Next, consider the requirements of “from host A’s subnet”. The problem statement tells you A’s IP address/mask (10.1.1.1/24). You need to somehow match all addresses in the resident subnet, and put that in the source IP address field of the command. Specifically, it needs to be a permit command (that part’s pretty obvious.) So, just from that analysis, the command will start as follows:
permit <protocol> 10.1.1.0 0.0.0.255
Matching Transport Ports
So far, the source address field matches all packets with source IP address in subnet 10.1.1.0/24. Looking further, the requirements mention “web services on server S4”. If the wording had simply stated “server S4”, I personally would interpret that to mean that we should match IP packets sent to that server. But “web services…” tells me that we should filter TCP traffic to that host, specifically, to the well-known TCP port for web (port 80). You can match port 80, or use the “www” keyword, either way. And in this case, to match the port, note that you cannot use the protocol type of “IP”, because IOS requires us to use either “TCP” or “UDP” when matching port numbers. Here’s the updated command:
permit tcp 10.1.1.0 0.0.0.255 host 192.168.2.254 eq www
And that’s it. For these exercises, I will list a handful of problem statements and the diagram. Later, I’ll post the answers. Your job: do the drills, and if you have questions, ask them. (It really is ok to ask questions.)
Drill to Build Complete ACLs
To move beyond thinking about a single ACE in a single ACL, you have to start thinking about the order of ACEs in the ACL, how they might impact each other. You also have to think about the default action to deny all other traffic, and whether you need to configure an alternative permit statement at the end of an ACL, for instance, the commonly used explicit permit all with the named ACL command permit ip any any.
Some of the ACL drills ask you to make multiline ACLs. In particular, these exercises make you consider:
- Do my configuration commands match some of the same packets? If so, what’s the correct order to use when adding the ACEs to the ACL?
- What is the impact of the implicit deny all at the end of each ACL? Can you take advantage of it?
- Should you configure an explicit permit all at the end of the ACL?
Drill to Interpret ACEs in an Editor
A third style for these drills is to interpret what other ACLs would match. The idea is simple: the question blog post lists a series of ACEs, and you have to describe with words and numbers what types of packets would match that ACE. Basically, it’s what you would do on the exam when you see a pre-configured ACL in a Sim, Simlet, or multi choice question.
These drills also have a small twist: the problem statement says that the commands exist in a text editor. Why? Well, it is possible for you to paste the command into a router, and the router then changes the values in the address fields. For example, with an address and wildcard mask of:
10.1.1.0 0.0.0.255
The address range is 10.1.1.0 – 10.1.1.255. Simple enough.
However, if the command included an address field like this:
10.1.1.1 0.0.0.255
When the command was copied into configuration mode, the router does some math that determines that 10.1.1.1 is actually not the beginning number in that range of addresses, but 10.1.1.0 is. So, IOS would change the parameters to:
10.1.1.0 0.0.0.255
Basically, if the address in an address/wildcard pair does NOT list the first IP address in that range, then IOS changes the command to use the first number.
So, your job in these drills is to think about the address ranges, but also to predict whether the command has the correct first value in that range, and if not, state what that value should be.
Summary and Link to the Questions
That’s it! Go forth and practice. You can find the current set of ACL Drills at this link.

That was really helpful, thanks a lot.
Sure thing Osama!
Mr. Odom Thanks again for your lecture. When will post the answers for the questions related to this?
Hi Dexter,
My habit has been to put 2-3 days between the question and answer. That gives a little time for people to notice it online and take a look before being tempted to see the answer. At least that’s always been my logic! 🙂 I’ll probably roll a couple of Q/A pairs in the next two weeks.
Thanks for playing…
Wendell
Thanks for this, having studied ICND2 material for a long time, I was looking for an ACL refresher and this is just the ticket! Nice work!
Very helpful thank you!
[…] Look below the fold for the questions. For more information about how an ACL or ACE might change once copied into configuration mode on a router, check out the launch post for the ACL Drills in this blog. […]
[…] post lists the answers to ACL drill set 2. What’s that? Check out this post that explains the details. No stopwatch, no speed requirement for these, unlike the subnetting speed practice. Answers are […]
4.6 Configure, verify, and troubleshoot IPv4 standard numbered and named access list for
routed interfaces
Why are there extended ACL questions here?
Hi,
The ACL content has moved to and from ICND1 and ICND2 over the years. Also, from a learning perspective, learning extended ACLs vs. stopping with learning only standard ACLs only adds about 20% more effort to the learning process. so I choose to keep it all together to make the learning process better. But I agree, as literally stated, extended ACLs aren’t in the ICND1 exam topics.
Wendell
Hello Wendell
I noticed a small typo in the text: “drills to to think”
Another typo…
The scenario states the server’s IP address is 192.168.2.254 but the ACL is written with 1.254.
Thanks to you both! Fixed.
Hello Wendell,
Please I need your help in clarifying an example that you used in Vol 2 CCNA study guide. In page 37 example 2-3 you gave an alternative configuration for a standard acl on router 1. That configuration used outbound acl on R1’s F0/0 & F0/1 interfaces for traffic sourced from servers 1& 2.
My confusion is why outbound acl was used instead of inbound. If standard numbered acl only filters by source ip, how would enabling an outbound acl on those interfaces match traffic sourced from servers 1 & 2? I cannot wrap my head around how the traffic from those servers ip would be filtered on those interfaces if the traffic from the servers will never pass outbound on those interfaces. Did I miss the point? I thought traffic outbound from those interfaces will have source ip of A & C’s subnet with destination of servers 1 & 2 ip? Thank you
Tewa,
Sure.
Might I suggest the following? Re-draw the figure on a wide piece of paper, with on server S1, the two routers, and hosts A and B. Then draw a packet above S1, representing a packet sent by S1 to host A. Mark the source and destination address. Then draw arrow lines over the routers to show which inbound and outbound interfaces that packet will flow in or out, respectively, as it traverses right-to-left from server S1 to host A. Those interfaces include R1’s F0/0, outbound. I think if you do that you’ll answer your own question.
If not, note that if you do the above, the packet you draw, with source address 10.2.2.1 – S1’s address – remains the same for the entire trip. That packet eventually exits R1’s F0/0 interface, which Example 2-3 shows ACL 2 enabled. That’s the packet, the exit interface, and it has a source IP address of 10.2.2.1 that matches a permit command in the ACL.
Let me know if that works to connect the ideas or not.
Wendell
Thank you so much Wendell, I now see the logic.
By the way each time I see your response am blown away and am always filled with joy. That you take time out of your busy schedule to answer questions and support random people on their career journey is heart warming. Authoring books and having a blog to support readers is amazing! You didn’t have to do this but you do it anyway. Kind of reminds me of what God did for us by sending Jesus 🙂 May God bless you real good!
You’re welcome, Tewa. It’s a great season of the year to be reminded to be generous every day, even as we’re reminded of God’s generosity! Thanks much for the encouragement!